Introduction to 10.0.0.0 and Its Importance in Networking
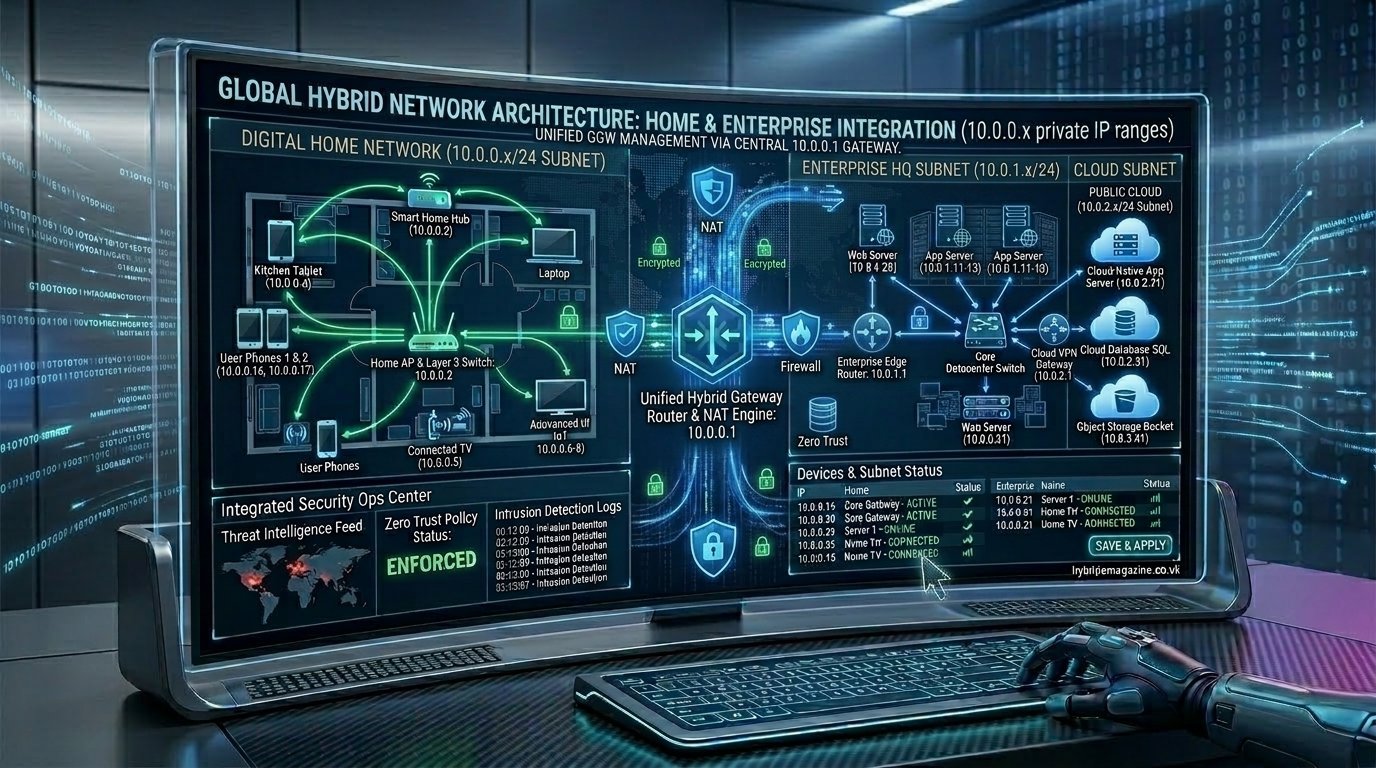
The 10.0.0.0 IP address range is one of the most important foundations of modern computer networking. It belongs to the private IPv4 address space, which is used internally within networks such as homes, offices, data centers, and cloud systems. Unlike public IP addresses, 10.0.0.0 is not routable on the internet, meaning it cannot be accessed directly from outside a local network.
This private addressing system exists to solve a major limitation of IPv4 called address exhaustion. Since the internet has far more devices than available public IP addresses, private ranges like 10.0.0.0 allow organizations to reuse internal IPs without conflicting with global routing systems. As a result, billions of devices can communicate efficiently through internal networks while sharing a smaller number of public IPs.
Understanding 10.0.0.0 is essential for anyone studying networking, cybersecurity, or IT infrastructure because it forms the backbone of local communication and routing logic in almost every digital environment today.
What is 10.0.0.0 IP Range and Private Addressing
The IP address 10.0.0.0 is not typically assigned to a single device. Instead, it represents the starting point of a large private network block that spans from 10.0.0.0 to 10.255.255.255. This entire range is reserved for internal use only, meaning it is invisible to the public internet.
Devices within this range receive addresses like 10.0.0.2, 10.0.0.10, or 10.0.5.25 depending on how the network is configured. These addresses allow devices to communicate with each other within the same private system, such as a home Wi-Fi network or an enterprise LAN.
The key idea behind this system is isolation. While millions of organizations may use the same 10.0.0.0 range internally, their networks remain separate and do not interfere with each other due to network translation systems and routing isolation.
RFC 1918 and Private IP Architecture
The 10.0.0.0 network is defined under RFC 1918, a technical standard created by the Internet Engineering Task Force (IETF). This standard introduced private IP addressing to ensure that IPv4 could continue supporting global internet growth despite its limited address space.
RFC 1918 defines three main private IP ranges: 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16. Among these, the 10.0.0.0 block is the largest, offering over 16 million possible addresses for internal use. This makes it especially useful for large-scale networks such as corporations, universities, and cloud infrastructures.
Private IP architecture is built around the idea of non-routability on the public internet. This means routers on the internet backbone automatically ignore these addresses, ensuring that internal traffic remains isolated and secure within private environments.
10.0.0.0/8 CIDR Block Explained in Depth
The notation 10.0.0.0/8 refers to the CIDR (Classless Inter-Domain Routing) representation of the network. The “/8” indicates that the first 8 bits of the IP address are fixed as the network portion, while the remaining 24 bits are available for host allocation.
This structure creates a massive address pool containing 16,777,216 possible IP addresses. Because of this size, network administrators often subdivide the range into smaller segments to improve organization and performance.
For example, instead of using the entire /8 block as one network, it is common to divide it into smaller CIDR blocks like /16 or /24 networks. This allows better control over traffic flow, improved security boundaries, and easier network management in complex infrastructures.
How Routers Use 10.0.0.0 Networks (DHCP and Gateway Systems)
In real-world environments, routers play a critical role in managing the 10.0.0.0 network. Most routers assign themselves an internal address such as 10.0.0.1, which acts as the default gateway for all connected devices. This gateway is responsible for directing traffic between the local network and external internet destinations.
Routers also use DHCP (Dynamic Host Configuration Protocol) to automatically assign IP addresses to devices. When a device connects to a network, the router dynamically provides an available IP address from the 10.0.0.0 range, ensuring smooth communication without manual configuration.
This automated system simplifies network management significantly, especially in environments with many connected devices such as offices, schools, and smart home systems.
Subnetting and Network Segmentation Inside 10.0.0.0
Subnetting is a core concept in managing large IP ranges like 10.0.0.0. It involves dividing a large network into smaller, more efficient segments called subnets. Each subnet operates as an independent network while still belonging to the same larger system.
In practical use, a network administrator might divide 10.0.0.0/8 into multiple smaller networks to separate departments or functions. For example, one subnet may handle employee devices, while another handles servers or guest Wi-Fi traffic.
This segmentation improves performance by reducing broadcast traffic and enhances security by isolating different parts of the network from each other. It also makes troubleshooting easier because issues can be identified within specific subnets rather than the entire network.
NAT and Internet Connectivity with 10.0.0.0
Since devices using 10.0.0.0 are not directly accessible from the internet, Network Address Translation (NAT) is used to enable communication with external networks. NAT allows multiple devices within a private network to share a single public IP address when accessing the internet.
When a device sends a request to a website, NAT translates its private 10.0.0.x address into a public IP address before the request reaches the internet. The response is then translated back so the correct device receives the data.
This system is essential for modern internet usage because it significantly reduces the number of public IP addresses required and adds a layer of security by hiding internal network structures from external users.
Security Benefits and Risks of 10.0.0.0 Networks
One of the strongest advantages of the 10.0.0.0 network is its inherent security through isolation. Since private IP addresses are not accessible from the public internet, external attackers cannot directly target devices within the network without passing through security layers like firewalls or VPN gateways.
This isolation helps protect sensitive data and internal systems from direct exposure. It is one of the reasons why almost every organization uses private IP addressing as part of its security strategy.
However, security risks can still exist inside the network. Misconfigured devices, weak authentication, or poor segmentation can allow unauthorized access within the internal system. Therefore, proper network design and monitoring are still essential even when using private IP ranges.
Common Issues: IP Conflicts, VPN Overlap, and Troubleshooting 10.0.0.1
Despite its advantages, the 10.0.0.0 network can sometimes create technical issues. One common problem is IP address conflict, which occurs when two devices are assigned the same IP address within the same subnet. This can lead to connectivity failures or unstable network behavior.
Another frequent issue appears in VPN connections. Many organizations use the same private IP range, so when two networks using 10.0.0.0 connect through a VPN, address overlap can cause routing confusion and broken communication paths.
Users also often encounter the address 10.0.0.1 when logging into router settings. This is typically the default gateway used for configuration, and troubleshooting it often involves checking DHCP settings, resetting the router, or verifying subnet masks.
Read more: 10.0.0
Real-World Usage in Enterprise, Cloud, ISP, and Home Networks
The 10.0.0.0 network is widely used across different environments, from small home setups to global enterprise systems. In home networks, it often serves as the default LAN configuration provided by routers for connecting personal devices.
In enterprise environments, 10.0.0.0 is used for large-scale internal communication systems that include thousands of devices, servers, and applications. These networks are carefully segmented and managed to ensure performance and security.
Cloud providers and ISPs also rely heavily on private IP addressing. Virtual private clouds, internal service meshes, and backend infrastructures often use 10.0.0.0 ranges to maintain isolated and scalable environments that support global services.
Conclusion
The 10.0.0.0 IP address range is a fundamental part of modern networking that enables efficient, secure, and scalable communication within private systems. Defined under RFC 1918, it provides millions of usable addresses that power everything from home Wi-Fi networks to massive cloud infrastructures.
By combining subnetting, NAT, DHCP, and routing techniques, the 10.0.0.0 network allows devices to communicate seamlessly while remaining isolated from the public internet. Despite occasional challenges like IP conflicts or VPN overlap, it remains one of the most reliable and widely used networking standards in the digital world.
Understanding 10.0.0.0 is essential for grasping how the internet functions behind the scenes, making it a key concept for students, IT professionals, and anyone interested in networking technology.